The Important Role of Password Policy in Protecting Data from Leaks
Read Time 5 mins | 21 Mar 2026 | Written by: Hastin Lia
Data security is one of the most important aspects for companies, organizations, and even individuals. One of the most basic ways to protect access to sensitive information is to implement a strong password policy. Passwords are often the first line of defense in a security system, and weaknesses in their use can lead to serious security breaches, including leaks of personal and company data.
This article will discuss the important role of password policies in protecting data from leaks, how effective password policies can be implemented, and why companies must always update and enforce these policies in the face of ever-evolving cyber threats.
1. The Importance of Password Policy in Data Security
Passwords serve as a barrier that protects sensitive data from unauthorized access. Without a good password policy, a company's systems and data are vulnerable to cyber attacks such as hacking, identity theft, and data leaks. A good password policy provides guidelines for employees on how to create, manage, and protect their passwords, thereby reducing the likelihood of successful cyber attacks.
A strong password policy should cover several important aspects, such as password length, character combinations, and password change frequency. In addition, this policy should consider how to protect passwords so that they are not easily guessed or obtained by unauthorized parties.
Read: 7 Effective Steps to Protect Company Data from Phishing and Malware
2. Threats Arising from Weak Passwords
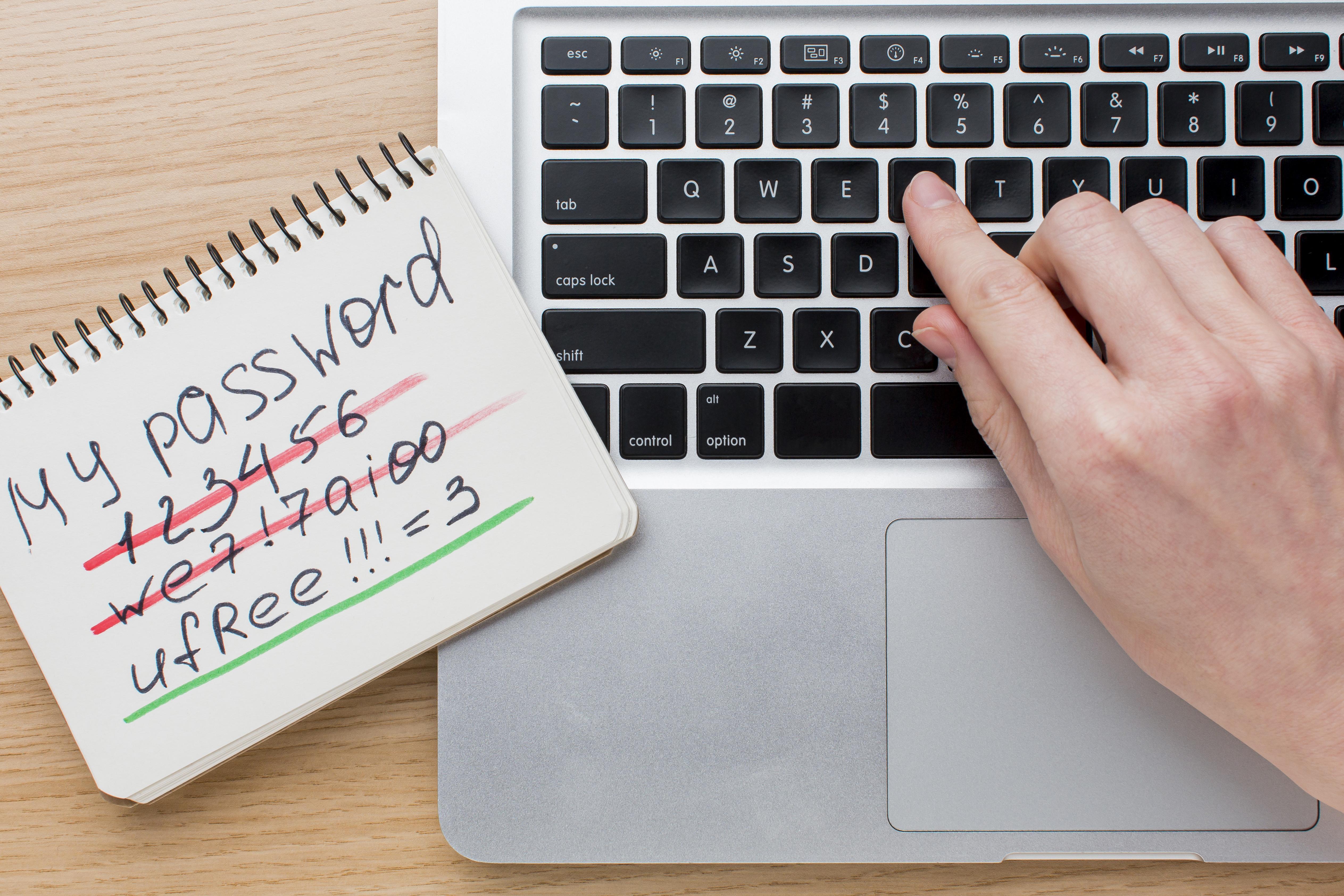
Weak passwords are one of the biggest vulnerabilities in a company's security system. Some examples of weak passwords include using short passwords, using personal names, or choosing passwords that are easy to guess, such as “123456” or “password.” The use of weak passwords opens up a huge opportunity for hackers to breach security systems and access sensitive data. There are several types of attacks that exploit weak passwords:
a. Brute Force Attacks
Brute force attacks involve the use of software that tries to guess every possible password combination until it finds the right one. If the password used is too short or simple, a brute force attack can quickly break into a user's account.
b. Phishing
Phishing attacks are one of the most commonly used methods for stealing passwords. Through fake emails or messages, hackers try to obtain user login information by posing as legitimate parties, such as banks or well-known service providers.
c. Credential Stuffing
Credential stuffing is a technique used by hackers to try to use leaked username and password combinations from one site to access user accounts on other sites. This often occurs when users use the same password for multiple accounts.
d. Man-in-the-Middle Attack (MitM)
In a MitM attack, hackers intercept communications between users and servers to steal login information, including passwords, without the user's knowledge. If encryption is not implemented, this attack can easily exploit this vulnerability.
3. Key Elements in an Effective Password Policy
To protect data from leaks, the password policy implemented by a company must have several key elements designed to strengthen protection against cyber attacks. Some of these elements include:
a. Password Length and Complexity
Longer and more complex passwords tend to be more difficult to guess or crack through brute force attacks. As a general guideline, passwords should consist of at least 8-12 characters, including a combination of upper and lower case letters, numbers, and symbols. This policy will ensure that passwords have a higher level of security than short and simple passwords.
b. Regular Password Changes
In addition to using strong passwords, changing passwords regularly is also very important for maintaining system security. A policy that requires employees to change their passwords every 60 or 90 days can prevent hackers from using login information they may have stolen.
c. Prohibition of Using the Same Password for Multiple Accounts
Using the same password across multiple platforms or applications is a very dangerous habit. If one account is hacked, all other accounts that use the same password will also be at risk. Company policies should emphasize the importance of using unique passwords for each account or system.
d. Use of Multi-Factor Authentication (MFA)
MFA is an additional layer of security that requires users to provide a second form of identification after entering their password. This can be in the form of a code sent to a mobile phone or token device. MFA makes hacking more difficult because hackers must not only steal the password, but also gain access to the additional authentication device.
e. Monitoring and Detection of Suspicious Activity
Companies should adopt technology that can detect suspicious activity, such as multiple failed login attempts or access attempts from unusual geographic locations. With real-time monitoring, threats can be identified earlier before a data breach occurs.
f. Employee Training and Awareness
Cybersecurity awareness should be an integral part of password policy. Employees need to be trained on how to create strong passwords, the importance of avoiding phishing, and how to keep their passwords confidential. This includes not writing passwords in places that are easily accessible to others or sharing passwords with anyone.
4. Steps to Implement an Effective Password Policy
Once you know the key elements of a strong password policy, the following steps can help your company implement it effectively:
a. Develop a Formal Policy
Your company should have a clearly documented security policy that includes guidelines on password creation, use, and management. This policy should include specific rules regarding password length, complexity, and frequency of replacement.
b. Use a Password Manager
To help employees manage complex and unique passwords, companies can provide password manager tools. These tools can securely store passwords and automatically generate strong passwords. This way, employees do not need to remember all their different passwords.
c. Using Encryption Technology
All passwords must be stored in encrypted form, so that if the data is stolen, hackers cannot easily use it. Strong encryption algorithms, such as bcrypt or SHA-256, must be used to protect employee login data.
d. Policy Enforcement and Monitoring
A strong password policy will not be effective if it is not consistently enforced. Companies must have a system in place to monitor compliance with this policy and take action in case of violations. In addition, monitoring should be conducted to detect suspicious login attempts or other security breaches.
e. Integrating with Multi-Factor Authentication (MFA)
A strong password policy must always be complemented by MFA. MFA provides an additional layer of protection that is highly effective in preventing unauthorized access even if passwords have been stolen. Integrating MFA into a company's system can significantly reduce the risk of data theft.
5. Facing Challenges in Implementing Password Policies
Although important, implementing strong password policies often faces several challenges. One of the main challenges is resistance from employees who may feel inconvenienced by overly complex password requirements or frequent password changes. To overcome this, companies need to educate employees about the importance of these policies in protecting them and the company from cyber threats.
In addition, companies need to develop tools that facilitate the implementation of password policies, such as password managers and MFA, so that employees do not feel burdened by additional security requirements.
6. Real Cases of Data Breaches Due to Weak Passwords
Various major data breaches have occurred due to the use of weak passwords or poor password management. One example is the Equifax data breach in 2017, where hackers managed to steal the personal data of more than 147 million people. One of the factors that led to this attack was a security vulnerability stemming from easily guessed passwords. This incident shows how important strong password policies are in preventing major losses.
Read: 10 Simple Steps to Protect Your Business Data
Conclusion
A strong password policy is an important component of a company's cybersecurity strategy. With cyber threats on the rise, weak passwords can be a major vulnerability exploited by hackers to steal company data or customers' personal information. Therefore, companies must ensure that they implement effective password policies, which include password length and complexity, regular password changes, the use of MFA, and employee training on cybersecurity awareness. With these measures, companies can significantly reduce the risk of data breaches and protect their assets from evolving cyber threats.
